Looking at it from another angle, a website is a primary touchpoint between business and customer, and the most visited source of information about an organization. A CMS helps keep it up-to-date and offers interactive functionalities to engage visitors with content. It can also become a repository of preferences, opening ways for content personalization. Therefore, a CMS may have a powerful impact on lead nurturing and conversion.
Overhead reduction and visitor’s experience are paramount, but so is security. Prevention of malicious attacks in each organization is a result of a carefully thought-through strategy. A safe CMS is an integral part of it.
With this in mind, we looked into different types of content management systems to understand how they balance efficiency, functionality, and security.
1. Full-fledged applications
A) Installed applications
Ready-to-install, full-fledged applications, such as WordPress, Joomla, or Drupal, are the most popular choice of CMS. As of March 2021, together they cover 70% of the market.
Simple and intuitive, WordPress is a popular choice for blogs or small ventures’ websites, but that’s not a rule: The White House also runs on this CMS. Joomla, on the other hand, is a go-to choice for e-commerce or social networking projects. Meanwhile, Drupal allows building highly configurable business websites, yet it comes with a “price”: technical knowledge. Some customizations might need a light HTML or CSS touch. If drag & drop behaviors don’t suffice, you have to build additional functionalities in PHP. Without a fair evaluation of your needs and resources, this might lead to getting lost in overhead. Drupal-run websites include Tesla and NASA.
To extend software features, all three come with themes (for appearance) and plugins/modules (for other purposes – SEO, analytics, forms… If you want to replace the old text CAPTCHAs with a witty puzzle, there’s a plugin for that, too).
As open-source platforms, this type of CMS is both developed and hacked by many. For example, WordPress accounts for roughly 90% of all hacked sites. It is important to remember that to offer easy installation and one-click upgrades, these applications need a very wide access to the database and filesystem, which is a serious security concern. Out of the three, Drupal comes off as the most security-oriented system due to its proactive, tech-savvy users and frequent security patches.
B) Applications based on a major framework
This type of CMS is based on an open-source framework with a set of reusable components for web development. The most sought-for frameworks are Laravel and Symfony. While the former is well-known for its simple coding and short development time, the latter is often perceived as more reliable and fit for complex projects.
The market share of these content management systems is very small. Take Sulu, October CMS, and TypiCMS as an example: together, they don’t even cover 1%. Yet they are often adopted by web development agencies and digital studios, working with different customers and their specific needs. Having similar features as Joomla or Drupal, these applications additionally benefit from the framework’s architecture. It gives more power to build custom components, integrate the CMS with other applications built on the same framework, and if needed, reuse codes from project to project.
In comparison to installed CMS applications, the framework-based apps do not require wide-reaching access to the database or filesystem. It is limited to specific areas and behaviors, bringing more security. On the other hand, they are rather dependent on the vendor’s decisions, posing a risk of breaking framework changes with major releases. However, while minor releases may come out as often as every week, both Laravel and Symfony separate paradigm-shifting changes by years.
2. Custom CMS
The term is self-explanatory: a custom CMS is exclusive for a specific use case and provides full control over its functionalities, looks, and updates. Bespoke development offers considerably higher integration and extensibility than any other application could offer out-of-the-box. Despite that, it does not imply that all custom CMS are built from scratch. In most cases, they are developed based on a known framework (Laravel, Symfony), while the actual tailor-made aspects are data model and user interface.
Although custom systems require manual updates, the framework with most of the required elements in place prevents their complexity.
Being flexible, such systems can be easily adapted to required security standards. As long as it’s not related to the framework in use, the custom-built CMS are unsusceptible to high-security threats. However, as many organizations delegate custom development to third parties, it is recommended to carefully review their security policies and best practices before starting a collaboration.
3. Static site generators
Static site generators (SSG) offer a no-sweat and zero overhead content management process. Raw data is applied to pre-made templates and generated to a view (landing page). They can be installed and then used from a central point, for example, an intranet server.
Because of reduced site complexity, SSG are appreciated for speed, reliability, and smooth developer experience. It’s a perfect choice for anyone who only needs a presentation layer, and is not planning on having many editors doing several edits on multiple pages. A good example of an SSG use case is a designer portfolio without dynamic content.
Static assets can be served from a simplified web server or directly from a content delivery network. Combined with no need to access databases, it makes a security-tight tool.
–
While there’s no one-size-fits-all formula for the best content management system, every organization – from small business to enterprise – should make their decision after evaluating the following:
- The time and resources a CMS requires
- The functionalities it covers
- Compliance with organization’s security standards
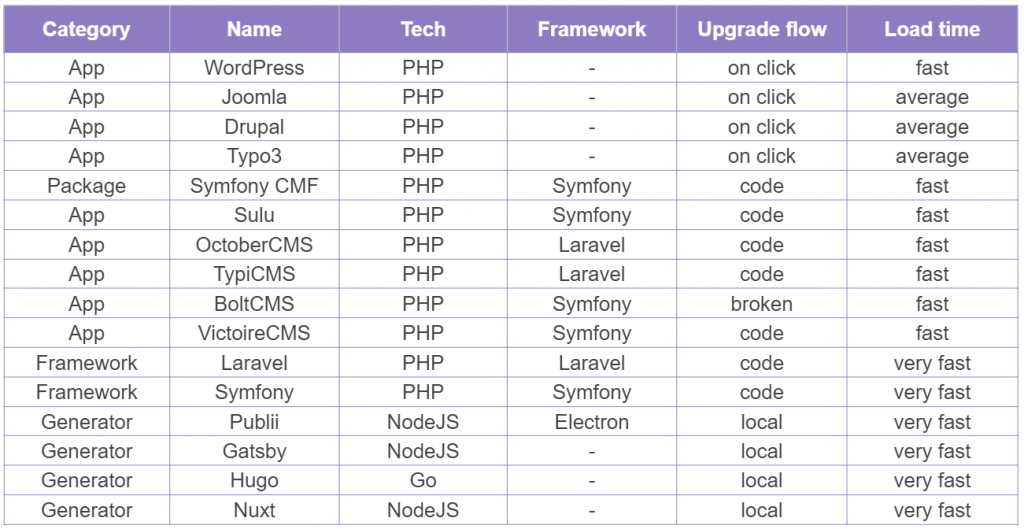
For readers looking for more technical insight, we prepared a comparison table between some of the most well-known, content management systems of different types: